- Visitor logs contain personal data that triggers GDPR, CCPA, and other privacy laws
- No single "correct" retention period exists; it depends on jurisdiction and purpose
- Automate deletion workflows or you'll forget, and regulators won't
- Audit trails prove compliance; paper logbooks prove nothing
- A written retention policy is the cheapest insurance you'll ever buy
Every time a visitor signs in at your front desk, you're collecting personal data. Name, email, photo, host name, time of arrival, maybe even a government ID scan. Most workplace teams don't think twice about it. Regulators do.
Visitor data retention sits at the intersection of workplace operations, legal compliance, and IT security. Get it wrong and you're looking at fines, reputational damage, or both. Get it right and it becomes one of those invisible processes nobody notices, which is exactly the point.
This guide covers what visitor data actually triggers privacy regulations, how long you can keep it by jurisdiction, how to build deletion workflows that don't rely on someone remembering, and a policy template you can adapt today.
What visitor data triggers privacy regulations
Not all visitor data is created equal. A first name scribbled in a paper logbook is different from a photo ID scan stored in a cloud database. But under most modern privacy frameworks, both count as personal data.
The data you're probably collecting
Most visitor management systems capture some combination of the following: full name, email address, phone number, company affiliation, host employee name, photo (either uploaded or captured at check-in), ID document details, visit purpose, and timestamps. Some systems also log Wi-Fi MAC addresses or require health screening responses.
Under GDPR's definition of personal data, any information that can identify a natural person, directly or indirectly, qualifies. That includes a visitor's name paired with a timestamp. Under California's CCPA framework, the definition is similarly broad, covering identifiers like name, email, IP address, and biometric data.
The practical implication: if your visitor sign-in process collects anything beyond an anonymous headcount, you're handling regulated data. Period.
Why paper logbooks are a compliance liability
Paper logbooks feel low-tech and therefore low-risk. They're neither. Every visitor who signs in can see the names, companies, and arrival times of everyone who signed in before them. That's a data exposure event happening dozens of times per day.
You also can't automate deletion of a paper logbook. You can't run an audit query against it. You can't prove to a regulator exactly when a record was created or destroyed. If your organization still relies on paper, your visitor management approach needs an upgrade before anything else in this guide matters.
Biometric and ID data raise the stakes
Several U.S. states have biometric privacy laws. Illinois' BIPA is the most aggressive, requiring written consent before collecting fingerprints, facial geometry, or retina scans. BIPA violations carry statutory damages of $1,000 to $5,000 per incident. If your lobby kiosk captures visitor photos and stores them as facial templates, you may be in scope.
The takeaway isn't "don't collect biometric data." It's "know exactly what you're collecting, why, and for how long."

Paper logbooks expose visitor data to everyone in the lobby. A digital system controls who sees what, automates consent capture, and creates the audit trail regulators expect. See how leading workplace teams handle it.
Read the guide
Retention period guidance by jurisdiction
Here's the question every workplace leader asks: "How long can we keep visitor records?" The honest answer is frustrating. It depends.
No major privacy regulation prescribes a single, universal retention period for visitor data. Instead, they establish principles. You keep data only as long as necessary for the purpose it was collected. Once that purpose expires, the data goes too.
GDPR (EU/EEA And UK)
GDPR's storage limitation principle requires that personal data be kept "no longer than is necessary for the purposes for which the personal data are processed." For visitor logs, the typical justification is building security and safety compliance.
Most EU data protection authorities suggest visitor data retention of 30 to 90 days for standard security purposes. The French CNIL has recommended that visitor access logs be retained for no more than three months unless a specific legal obligation requires longer. If you're retaining visitor records for six months "just in case," you need a documented justification or you're non-compliant.
Key GDPR requirements for visitor data:
- Lawful basis: Legitimate interest (building security) is the most common basis. Consent works but creates operational headaches if visitors withdraw it.
- Transparency: Visitors must be told what data you collect, why, and how long you keep it, before or at the point of collection.
- Data subject rights: Visitors can request access to their records, correction, or deletion. You need a process to handle these requests within 30 days.
For a deeper look at how GDPR intersects with workplace data collection, our GDPR workplace analytics guide covers the broader compliance picture.
CCPA/CPRA (california)
California's privacy framework doesn't specify retention periods either, but the CPRA amendments added a data minimization requirement: businesses must limit collection and retention to what's "reasonably necessary and proportionate" to the stated purpose.
For visitor data, this means:
- Disclose at collection what categories of data you're gathering and why
- Don't retain visitor records longer than the security purpose requires
- Honor deletion requests from California residents (with limited exceptions for security investigations)
A 90-day retention window is defensible for most organizations. Anything beyond that needs a specific, documented reason.
Other jurisdictions worth watching
Brazil (LGPD): Mirrors GDPR's purpose limitation and storage limitation principles. Visitor data should be deleted when the processing purpose ends.
Canada (PIPEDA): Requires that personal information be retained "only as long as necessary for the fulfillment of those purposes." The Office of the Privacy has issued guidance suggesting organizations establish maximum retention periods and stick to them.
Singapore (PDPA): Organizations must cease retaining personal data when it's no longer needed. The Personal Data Protection Commission has been active in enforcement.
U.S. state patchwork: Beyond California, states like Virginia (VCDPA), Colorado (CPA), Connecticut, and others have enacted privacy laws with varying data minimization requirements. If you operate across multiple states, your retention policy needs to account for the strictest applicable standard.
Practical retention period recommendations
The pattern is clear: shorter is almost always safer. When in doubt, delete sooner.Understanding your compliance standards across all workplace operations, not just visitor management, helps you build a consistent framework rather than a patchwork of one-off policies.
Audit trails and deletion workflows
A retention policy without an enforcement mechanism is just a document. The gap between "we have a policy" and "we follow the policy" is where most organizations get into trouble.
What an audit trail needs to capture
For visitor data, your audit trail should record:
1. Collection event: When the data was captured, what was collected, and the lawful basis or consent record 2. Access events: Who viewed the visitor record and when (especially important for security investigations) 3. Retention clock: The scheduled deletion date based on your retention policy 4. Deletion event: Confirmation that the record was actually destroyed, including timestamp and method
If your current system can't produce this information on demand, you'll struggle during a regulatory audit or data subject access request. This is one area where workplace security policies and visitor management need to be tightly aligned.
Automating deletion: The only reliable approach
Manual deletion processes fail. Not because people are careless, but because deleting old visitor records is never anyone's top priority. It sits on a to-do list until an auditor asks about it.
Automated deletion works like this:
- Each visitor record gets a retention expiry date at the moment of creation, based on your policy rules
- The system runs a scheduled job (daily or weekly) that identifies expired records
- Expired records are permanently deleted, not archived, not moved to a "deleted" folder
- The deletion event is logged in the audit trail
Some organizations need a "soft delete" grace period where records are flagged for deletion but recoverable for a short window (7-14 days) before permanent destruction. That's fine, as long as the grace period is documented and the final deletion is automatic.
Handling deletion exceptions
Not every record can follow the standard retention schedule. Security incidents, legal holds, and regulatory investigations all create legitimate reasons to extend retention. Your workflow needs an exception process:
- Legal hold: When counsel issues a litigation hold, affected visitor records must be preserved regardless of the standard retention schedule. Tag these records and exclude them from automated deletion.
- Security investigation: If a visitor record is relevant to an active investigation, extend retention until the investigation closes. Document the reason and the approving authority.
- Data subject request: Under GDPR, a visitor can request deletion before your standard retention period expires. You must comply within 30 days unless a legal exception applies.
The key is that exceptions are documented, time-bound, and reviewed regularly. An exception that lasts forever isn't an exception; it's a policy failure.
Gable's office management tools handle visitor check-in, data capture, and access logging in a single system, giving you the audit trail and control that compliance requires without adding friction for visitors or front desk teams.
See how it works
Building your visitor data retention policy
A retention policy doesn't need to be 40 pages. It needs to be clear, enforceable, and accessible to the people who handle visitor data daily. Here's a template framework you can adapt.
Policy template structure
1. Scope Define what this policy covers. All personal data collected from visitors to company premises, including but not limited to: name, contact information, identification documents, photographs, health screening responses, and access logs.
2. Data collected and purpose List each data element, why you collect it, and the lawful basis:
3. Retention periods Specify the retention period for each data category. Reference the table from the previous section. Be explicit: "Standard visitor records are retained for [X] days from the date of the visit and then permanently deleted."4. Deletion procedures Describe how deletion happens. Automated system purge on a defined schedule. Manual deletion process as a backup. Audit log of all deletion events.
5. Exceptions Document the process for legal holds, security investigations, and data subject requests. Name the role (not the person) authorized to approve exceptions.
6. Data subject rights Explain how visitors can exercise their rights: access, correction, deletion, portability. Include contact information for your privacy team or DPO. Specify response timelines (30 days under GDPR, 45 days under CCPA).
7. Third-party processors If your visitor management system is cloud-hosted (most are), identify the processor and confirm a Data Processing Agreement is in place. This matters because your vendor's data retention practices become your compliance problem.
8. Review schedule Commit to reviewing the policy at least annually or when regulations change. Name the responsible team.
Making the policy operational
A policy document sitting in a SharePoint folder doesn't protect you. Operationalizing it means:
- Training front desk staff on what data they can and can't collect, and what to say when visitors ask about privacy
- Configuring your visitor management system to enforce retention periods automatically
- Adding privacy notices to your visitor check-in flow, whether that's a digital kiosk, a pre-registration email, or signage in the lobby
- Running quarterly audits to verify that deletion is actually happening on schedule
Your workplace compliance program should treat visitor data retention as a standing audit item, not a one-time checkbox.
Common mistakes to avoid
Over-collecting data. If you don't need a visitor's phone number, don't ask for it. Every data point you collect is a data point you have to protect, retain appropriately, and eventually delete.
Using visitor data for marketing. This is a consent minefield. Unless you have explicit, freely given consent (not a pre-checked box buried in your sign-in flow), don't add visitors to marketing lists. Under GDPR, this is almost certainly a violation.
Treating all visitors the same. A delivery driver dropping off a package has different data requirements than a board member attending a quarterly meeting. Your policy should differentiate between visitor types and apply proportionate data collection.
Ignoring employee privacy in the process. Visitor records often include the host employee's name and department. That's employee personal data too. Your employee privacy framework needs to account for this overlap.
How visitor data retention fits into your broader workplace strategy
Visitor data retention isn't an isolated compliance exercise. It connects to how you think about workplace security, space planning, and the overall experience you create for everyone who walks through your doors.
The data you collect from visitors, when aggregated and anonymized, can tell you things about your space that occupancy sensors miss. Which days have the most external meetings? Are certain conference rooms disproportionately used for client visits? Is your lobby designed to handle peak visitor volume on Tuesdays and Wednesdays?
These insights matter for right-sizing your office space and for designing a visitor experience that reflects well on your company. But you can only extract these insights if your data practices are clean. Hoarding raw visitor records for years doesn't give you better analytics. It gives you a compliance liability and a messy dataset.
The smart approach: collect what you need, retain it for a defensible period, extract anonymized insights for space planning, and delete the personal data on schedule. That's how you turn visitor management from a compliance headache into a source of operational intelligence.
Your workplace security posture also benefits from clean data practices. When you know exactly what visitor data you have and where it lives, you can protect it more effectively. When you don't, every undeleted record is an attack surface.
From visitor check-in to space utilization analytics, Gable gives you the tools and data to run a workplace that's compliant, efficient, and worth showing up to. Book a demo and see it in action.
Book a demo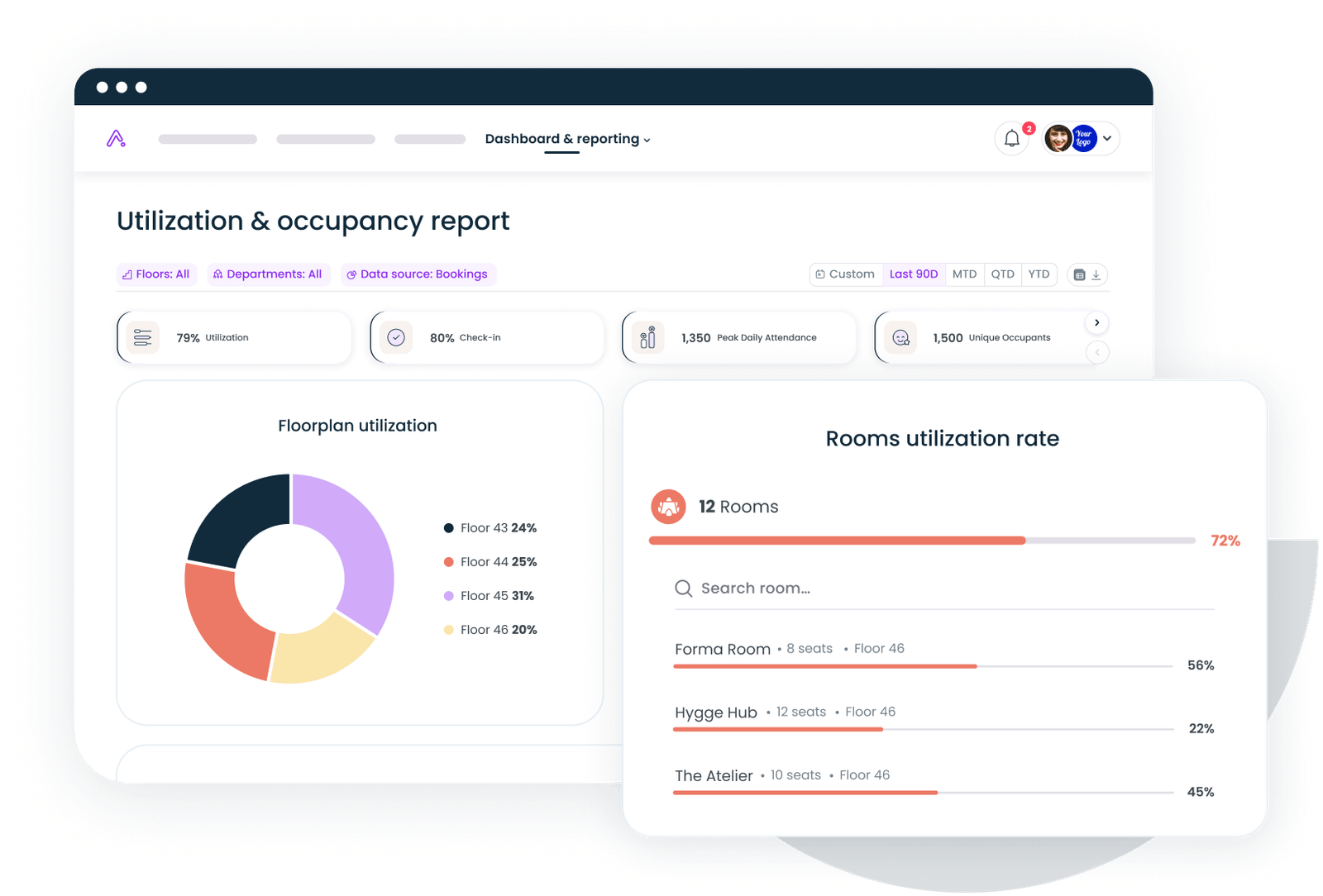




.svg)





.svg)