- Office security spans three pillars: physical access control, cybersecurity, and procedural safeguards, and all three need to work together in hybrid environments.
- Hybrid work creates unpredictable occupancy patterns that make traditional security systems inadequate; integrated booking and badge data closes the gap.
- AI-powered security tools are reducing workplace incidents by 25-30% for organizations that adopt them.
- Workplace violence remains a serious threat, with 740 fatal violent acts recorded in U.S. workplaces in 2023 alone.
- Balancing employee privacy with security monitoring is a defining challenge for workplace leaders this year.
Every workplace leader faces the same tension: you need to keep people safe without turning the office into a fortress that nobody wants to visit. That tension has only grown more complex as hybrid work reshapes who's on-site, when, and why.
The numbers tell a clear story. According to Kastle Systems, 97% of workers now prioritize feeling safe when choosing an employer, and 89% of Americans say they value workplace safety more than ever. Meanwhile, 72% of security decision-makers report that risk has never been higher, up from 55% in 2024.
Office security isn't a single system or a checklist you complete once a year. It's an ongoing practice that connects physical infrastructure, digital defenses, employee behavior, and the technology that ties them all together. This guide breaks down what a comprehensive office security program looks like in 2026, with data-backed frameworks you can put into action.
The three pillars of office security
A strong office security program rests on three interconnected pillars: physical security, cybersecurity, and procedural safeguards. Weakness in any one area creates vulnerabilities across the others.
Physical security
Physical security covers everything that controls who can enter your space and what they can access once inside. This includes:
- Perimeter controls: Locked entrances, security cameras, alarm systems, and adequate exterior lighting
- Access control systems: Badge readers, biometric scanners, mobile credentials, and QR/NFC-based entry
- Interior protections: Secure server rooms, locked filing cabinets, restricted zones for sensitive areas
- Surveillance: Camera systems with recording capabilities and, increasingly, AI-powered monitoring
The shift to hybrid work has made physical security harder to manage. When occupancy fluctuates daily, traditional approaches like staffing a front desk for a full building fall apart. A physical access control system (PACS) that integrates with your workplace management platform gives you real-time visibility into who's on-site without requiring manual headcounts.
Cybersecurity
Digital threats have escalated sharply. Half of companies now report an uptick in AI-generated phishing, malware, and identity fraud. And the human element remains the weakest link: according to Verizon's 2024 Data Breach Investigations Report, the human element is involved in 68% of breaches.
Office cybersecurity includes:
- Network security: Firewalls, encrypted Wi-Fi, VPN requirements for remote access
- Endpoint protection: Managed devices, automatic updates, mobile device management (MDM)
- Data protection: Encryption at rest and in transit, role-based access to sensitive files, regular backups
- Identity management: Multi-factor authentication, single sign-on (SSO), and regular credential audits
Procedural safeguards
Technology alone won't protect your workplace. You need documented policies, trained employees, and consistent enforcement. Procedural safeguards include security policies and procedures that cover everything from visitor screening to incident response, along with regular training and drills.
Physical access control in a hybrid workplace
Hybrid work has fundamentally changed the access control challenge. When you don't know who's coming in on any given day, traditional door-centric systems fall short. Unpredictable occupancy patterns raise both risk and cost.
Modern access control technologies
Today's badge access control systems go well beyond the plastic key card. Modern PACS options include:
- Mobile credentials: Employees use their smartphones to tap in, eliminating lost-badge issues and enabling instant credential revocation
- QR and NFC scanning: Quick entry via phone scan, particularly useful for visitors and temporary access
- Biometric readers: Fingerprint or facial recognition for high-security zones
- Cloud-based management: Admins can grant, modify, or revoke access remotely in real time
Connecting access control to occupancy data
The real power of modern access control comes from integration. When badge data connects to desk booking and room reservation systems, you get a complete picture of who's on-site and where they are. This matters for daily operations, but it becomes critical during emergencies.
For example, if your desk booking system shows 47 employees reserved spaces on Tuesday, and your badge logs confirm 43 actually entered the building, you've got an accurate headcount for evacuation purposes. That's a significant improvement over relying on calendar entries or manual sign-in sheets.
Gable's office management platform integrates with access control systems like Brivo, combining badge data with desk bookings and visitor check-ins to give workplace teams a unified occupancy view, so security and operations teams work from the same data.

Understanding who's in your office, when, and how spaces are used gives security teams the data they need to allocate resources effectively. Learn how workplace analytics deliver measurable ROI.
Read the guide
Visitor management as a security layer
Your visitor management system is your first line of defense against unauthorized access. Every person who walks through your doors and isn't a badged employee represents a potential security gap.
What effective visitor management looks like
A strong visitor management system should include:
- Pre-registration: Hosts invite visitors in advance, providing security teams with expected arrival information
- Identity verification: Photo ID checks, either manual or automated, at sign-in
- Document signing: NDAs, safety waivers, or other required documents completed during check-in
- Badge printing: Temporary badges that clearly identify visitors and their authorized areas
- Host notifications: Automatic alerts to the host employee when their guest arrives
- Blocklist screening: Cross-referencing visitor names against restricted-access lists
- Complete audit trail: A timestamped record of every visitor entry and exit
Integrating visitor data with workplace security
Visitor management becomes far more valuable when it's connected to your broader workplace systems. When visitor check-ins, employee badge data, and desk bookings all feed into a single dashboard, security teams can see total on-site headcount at any moment, not just employee data.
This integration also supports compliance requirements. Many industries require detailed records of who accessed specific areas and when. A unified system generates those records automatically.
Workplace violence prevention
Workplace violence is a persistent and serious threat that many office security plans underaddress. According to OSHA data, 740 of 5,283 fatal workplace injuries in 2023 were due to violent acts, with homicides accounting for 61.9% of those incidents. In 2021-2022, assaults resulted in 57,610 injuries, and 525 fatalities were reported in 2022 alone.
Building a prevention framework
The American Society for Industrial Security (ASIS) provides standards for policies, processes, and protocols to identify, assess, respond to, and mitigate threatening behavior. A workplace violence prevention program should include:
- Zero-tolerance policy: Clearly communicated to all workers, visitors, clients, and contractors
- Threat assessment team: A cross-functional group trained to evaluate and respond to warning signs
- Reporting channels: Anonymous and non-anonymous options for employees to flag concerns
- De-escalation training: Regular training for managers and front-line staff
- Coordination with law enforcement: Established relationships and communication protocols with local authorities
The role of technology in prevention
Access control and visitor management systems play a direct role in violence prevention. Blocklist screening catches individuals who've been flagged. Badge access logs create accountability. And real-time occupancy data helps security teams respond faster when incidents occur.
Knowing exactly who's in the building, and where, can make the difference between a contained incident and a catastrophe.
Ai-powered security: What's practical in 2026
AI is reshaping office security, but the practical applications matter more than the hype. Organizations deploying AI safety platforms report 25-30% fewer workplace incidents and 40% faster audit preparation.
Where AI adds real value
- Anomaly detection: AI systems can flag unusual access patterns, like an employee badging in at 3 AM when they've never worked nights, or a badge being used at two locations simultaneously
- Predictive occupancy analysis: By analyzing historical badge and booking data, AI can predict high-traffic days and help security teams staff accordingly
- Video analytics: Camera systems with AI can detect tailgating (unauthorized people following badged employees through doors), unattended packages, or unusual crowd patterns
- Automated compliance reporting: AI can compile access logs, incident reports, and audit trails into formatted reports, cutting hours of manual work
Keeping humans in the loop
AI works best as an augmentation layer, not a replacement for human judgment. Automated systems should flag anomalies for human review, not make autonomous security decisions. This is especially important for avoiding false positives that could create a surveillance-heavy culture.
The balance between workplace sensors and privacy is one that every organization needs to navigate carefully. Transparent policies about what's monitored, why, and who has access to the data are essential for maintaining employee trust.
Gable Offices combines desk booking, room scheduling, visitor management, and access control integration into one platform, giving workplace teams complete visibility into how spaces are used.
Learn more
Cybersecurity for the modern office
The cybersecurity landscape in 2026 demands more than firewalls and antivirus software. AI-generated threats are more sophisticated, attack surfaces have expanded with hybrid work, and the cost of breaches continues to climb.
Priority areas for office cybersecurity
Network segmentation and access
Separate your guest Wi-Fi from your corporate network. Segment sensitive systems (HR data, financial records, security cameras) onto isolated networks. Require VPN connections for any remote access to internal systems.
Identity and access management
Multi-factor authentication should be mandatory for every system, not optional. Implement role-based access controls so employees can only reach the data and systems they need for their jobs. Conduct quarterly access reviews to remove permissions for departed employees or changed roles.
Employee security training
Since the human element is involved in the majority of breaches, training is your highest-leverage investment. Effective programs are:
- Continuous: Monthly micro-trainings, not annual compliance checkboxes
- Interactive: Simulated phishing exercises with immediate feedback
- Tailored: Different content for executives (targeted spear-phishing), finance teams (invoice fraud), and general staff (password hygiene)
Incident response planning
Document your response plan for different scenarios: data breach, ransomware, physical intrusion, insider threat. Assign clear roles. Run tabletop exercises quarterly. The worst time to figure out your response plan is during an actual incident.
Coordinating security with hybrid schedules
One of the biggest workplace security awareness challenges in hybrid environments is the gap between who's expected on-site and who's actually there. This gap creates problems for emergency response, resource allocation, and threat detection.
Using booking data for security planning
When employees book desks and rooms through a centralized system, workplace teams gain advance visibility into expected occupancy. This data enables:
- Staffed security proportional to headcount: Don't pay for full-building security on a day when only 30% of desks are booked
- Proactive access management: Enable badge access for specific floors or zones based on who's booked to be there
- Accurate emergency rosters: Know exactly who should be in the building for evacuation accountability
- Anomaly detection: Flag when someone badges in who hasn't booked a space, or when a booked employee doesn't show up
Coordinating in-office days with security protocols
If your organization designates specific team days (e.g., engineering on Tuesdays, marketing on Thursdays), you can align security resources accordingly. High-occupancy days might warrant additional front-desk staff, while low-occupancy days might trigger different access protocols for after-hours zones.
Balancing security and employee privacy
According to Omnilert's research, workplace safety and employee privacy are interdependent: people feel safest where they feel both protected and respected. Push too hard on monitoring, and you'll erode the trust that makes your security program effective.
Principles for responsible security monitoring
- Transparency: Tell employees what's being monitored, why, and who can access the data. No hidden cameras, no secret tracking.
- Proportionality: Monitor what's necessary for safety, not what's convenient for management. Badge access logs serve a clear security purpose; tracking bathroom breaks doesn't.
- Data minimization: Collect only what you need. Set retention policies and stick to them. Delete data when it's no longer required.
- Role-based access: Limit who can view security data. Not every manager needs access to badge logs.
- Employee input: Include employee representatives in security policy development. Policies created without input tend to generate resistance.
For a deeper look at navigating employee privacy and workplace technology, including specific frameworks for different monitoring types, workplace leaders should establish clear governance before deploying new security tools.
Data-driven security audits
Physical access control systems generate valuable data about the flow of employees and visitors through your space. This data serves as a roadmap for decisions ranging from daily management to real estate choices and safety protocols.
What to audit and how often
| Audit Area | Frequency | Key Metrics |
|---|---|---|
| Access control logs | Monthly | Unusual access patterns, failed entry attempts, after-hours access |
| Visitor records | Monthly | Volume trends, screening compliance, average visit duration |
| Incident reports | Quarterly | Incident types, response times, resolution outcomes |
| Cybersecurity posture | Quarterly | Phishing test results, patch compliance, access review completion |
| Emergency preparedness | Semi-annually | Drill participation rates, evacuation times, communication effectiveness |
| Policy compliance | Annually | Policy acknowledgment rates, training completion, vendor compliance |
Turning audit data into action
Raw data isn't useful until it drives decisions. After each audit cycle:
- Identify the top three findings by risk severity
- Assign owners and deadlines for remediation
- Track progress in your next audit cycle
- Report trends to leadership quarterly
Workplace analytics platforms can automate much of this data collection and reporting, freeing security teams to focus on analysis and response rather than spreadsheet management.
Emergency response planning
Every office needs documented, practiced emergency response procedures. The quality of your plan directly affects outcomes during critical incidents.
Core components of an emergency response plan
- Evacuation routes and assembly points: Clearly marked, regularly updated, and accessible to all employees including those with disabilities
- Communication protocols: How you'll notify employees during an emergency (PA system, mass text, app notification), and who's authorized to send alerts
- Role assignments: Floor wardens, first-aid responders, evacuation coordinators, and their backups
- Shelter-in-place procedures: For scenarios where evacuation isn't safe (active threat, severe weather, chemical release)
- Reunification process: How you'll account for everyone after an evacuation, including visitors
The occupancy data advantage
Integrated workplace systems give emergency responders a critical advantage: they know who's supposed to be in the building. When your desk booking system, badge access logs, and visitor management records all feed into one platform, you can generate an accurate headcount within seconds of an evacuation order.
This is a significant improvement over traditional methods, where floor wardens manually check offices and conference rooms, often missing people in restrooms, phone booths, or huddle rooms.
Building your office security plan: A step-by-step framework
Creating a comprehensive office security plan doesn't require starting from scratch. Follow this framework to assess your current state and build toward a stronger posture.
Step 1: Conduct a risk assessment
Walk your facility with fresh eyes. Identify entry points, blind spots in camera coverage, unsecured areas, and any gaps between your current controls and your actual risks. Include both physical and digital vulnerabilities.
Step 2: Document policies and procedures
Write clear, specific policies covering access control, visitor management, incident response, data protection, and workplace violence prevention. Avoid vague language. "Employees should be careful with sensitive data" is useless. "Sensitive documents must be stored in locked cabinets or encrypted digital folders with role-based access" is actionable.
Step 3: Deploy the right technology
Select systems that integrate with each other. Standalone tools create data silos that undermine your security posture. Prioritize platforms that connect access control, visitor management, desk booking, and occupancy analytics.
Step 4: Train everyone, continuously
Initial training during onboarding isn't enough. Run monthly security awareness micro-sessions, quarterly phishing simulations, and semi-annual emergency drills. Track participation and results.
Step 5: Monitor, audit, and improve
Security isn't a project with an end date. Establish regular audit cycles, review incident data, and update your plan based on what you learn. The threat landscape changes constantly; your security program should change with it.
Conclusion: security as a workplace experience investment
Office security in 2026 requires more than locks and cameras. It requires connected systems, trained people, and data-driven decision-making. The organizations that get this right don't treat security as a cost center; they recognize it as a direct investment in employee confidence, talent retention, and operational resilience.
The hybrid workplace has made security more complex, but it's also created an opportunity. When you integrate access control, visitor management, desk booking, and occupancy analytics into a unified platform, you don't just improve security. You gain visibility into how your spaces are used, which informs everything from real estate strategy to team collaboration.
Start with an honest assessment of where you are today. Identify your highest-risk gaps. And build a plan that connects your people, your spaces, and your data into a security program that protects without creating friction.
Gable's all-in-one workplace platform integrates desk booking, visitor management, and access control data to give you complete visibility into who's on-site and how your spaces are used.
Get a demo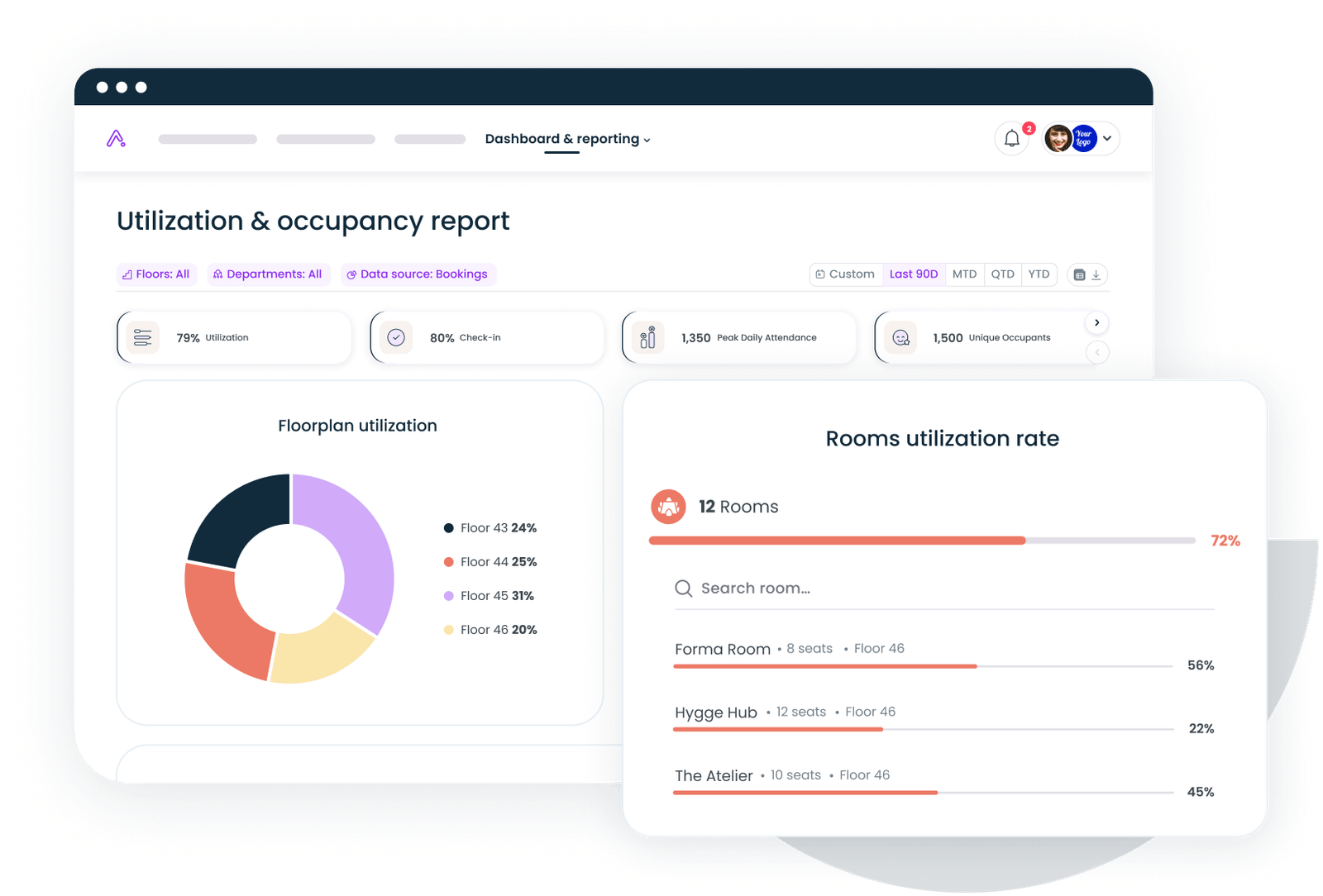





.svg)





.svg)